The Significance of Cyberattacks in 2023
The significance of cybersecurity has never been more pronounced than during 2023. With the global proliferation of technology and the digitalisation of almost every aspect, the risks have risen exponentially. Cyberattacks have emerged as a paramount concern, transcending mere data breaches and evolving into complex, multifaceted threats that can cripple nations and economies. The year 2023 marks a turning point where cyber warfare has become not just a buzzword but a daily reality. From government institutions to multinational corporations and small businesses, the spectre of cyberattacks looms large, threatening the very foundation of our interconnected world.
Growing Cyberattacks on Critical Infrastructure
In tandem with the growing significance of cybersecurity, the frequency and sophistication of cyberattacks on critical infrastructure have surged. This includes attacks on both private and public businesses that form the backbone of our society. Industries like energy, transportation, healthcare, and finance have witnessed a dramatic uptick in cyber intrusions.
Real instances of cyberattacks
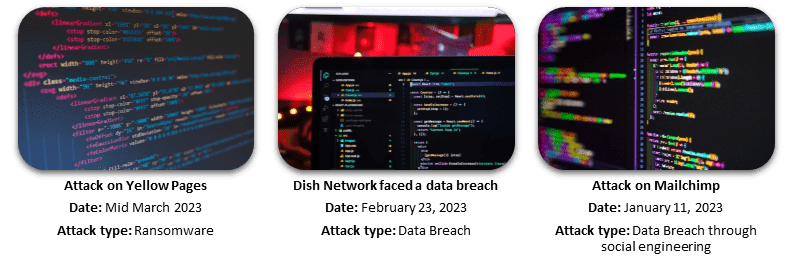
| Yellow Pages – No Industry is Immune | Dish Network – Disruption Beyond Data Theft | ||
| While Yellow Pages primarily provides access to publicly available information, beneath the surface, it stores sensitive personal data. The breach by the enigmatic entity known as Black Basta underscores the indiscriminate nature of these attacks. It’s a testament to the adaptability and persistence of cybercriminals who exploit any vulnerability they find. | The disclosure by Dish Network, one of the largest television providers in the USA, that a network outage was connected to a cyberattack sends shockwaves through the critical infrastructure landscape. While the root causes of the intrusion are still shrouded in mystery, the attack’s fallout was far from subtle. Data theft and an internal communication breakdown underscore the interconnectedness of critical infrastructure. Such attacks are a stark reminder that cyber threats are not confined to digital realms but can manifest as tangible disruptions, affecting the lives of countless individuals. | ||
| |||
The potential global consequences of cyberattacks on critical infrastructure are far-reaching and profound. When the systems that underpin our daily lives are compromised, the impact ripples outward, affecting not just the targeted organisations but entire communities, economies, and even national security. The data theft and internal communication breakdown that ensued are indicative of the chaos that can result from even a single attack.
Factors Contributing to Cyberattacks on Critical Infrastructure
In the year 2023, the threat landscape for critical infrastructure has evolved significantly, presenting an array of challenges that demand attention:
- Interconnectedness of systems and networks. In today’s hyperconnected world, where industries are interdependent, the notion of isolation has become obsolete. This interconnectedness, while fostering efficiency and collaboration, also serves as a double-edged sword. Cyber attackers often exploit these intricate connections to infiltrate otherwise secure systems. A breach in one sector can cascade through the entire ecosystem, affecting essential services and critical functions. To counteract this vulnerability, your business must adopt a comprehensive approach. This approach includes measures like network segmentation, which can isolate critical assets and reduce the attack surface, and continuous monitoring to swiftly identify and contain threats.
- Outdated systems within critical infrastructure. Many essential systems, such as those in power plants, water treatment facilities, and transportation networks, rely on legacy technology that was not designed with modern cybersecurity threats in mind. These outdated systems are often challenging to patch and update, leaving them exposed to known vulnerabilities. Addressing this challenge necessitates a commitment to modernisation. Investing in upgrading and replacing legacy infrastructure is crucial. Simultaneously, implementing stringent access controls is essential to limit exposure to potential threats.
- Human error remains a significant contributor to cyber incidents within critical infrastructure. Even in an environment that prioritises technology and automation, the role of human actors remains critical. Mistakes can happen at any level of an organisation, whether it’s an employee inadvertently clicking on a malicious link in a phishing email or misconfiguring a critical system. These errors can lead to security breaches with far-reaching consequences. Thus, a comprehensive risk management strategy should encompass robust employee training and awareness programs to reduce the likelihood of human errors. Additionally, your business should implement stringent access controls and role-based permissions to minimise the potential damage caused by human mistakes.
Risk Management Strategies for Cyberattacks on Critical Infrastructure
To combat these challenges effectively, your business must implement a multifaceted risk management strategy tailored to the evolving threat landscape.
- Prevention stands as the first line of defense. Proactive identification of vulnerabilities through regular security assessments and penetration testing is essential. A well-structured vulnerability management program helps prioritise and patch critical vulnerabilities promptly. Your organisation should also fortify their defenses with robust firewalls, intrusion detection systems, and advanced endpoint protection solutions to secure both the perimeter and internal networks.
- Detection is equally crucial, as timely identification of cyber threats minimises the potential damage. Deploying advanced threat detection tools like Security Information and Event Management (SIEM) systems can analyse network traffic and logs in real-time to spot suspicious activities. By using anomaly detection techniques, organizations can identify deviations from normal network behaviour, thereby raising red flags for potential breaches.
- However, even with the best preventive measures in place, incidents may still occur. Hence, a well-defined incident response plan becomes paramount (please check our Risk Management Strategies for Robust Disaster Recovery for further details regarding Incident and disaster recovery plans). This plan should outline clear procedures for reporting, containing, and mitigating incidents, as well as strategies for communication with stakeholders and regulatory authorities. Regularly rehearsing incident response scenarios through tabletop exercises ensures a swift and coordinated response when a real threat materialises.
- In addition to prevention, detection, and response, businesses must prioritizse resilience. Building cyber resilience involves designing systems and networks to withstand and recover from cyberattacks. This includes redundant systems, data backups, and robust disaster recovery plans. Your business should also consider adopting a zero-trust security model, which assumes that threats can exist both inside and outside the network. This approach requires continuous authentication and authorisation for all users and devices.
- Lastly, regulatory compliance plays a crucial role in the cybersecurity landscape of critical infrastructure. Many sectors are subject to industry-specific regulations and standards, such as the NIST Cybersecurity Framework or ISO 27001. Compliance with these frameworks provides a structured approach to managing cybersecurity risks and ensures that your business is aligned with industry best practices.
In conclusion, mitigating the risks posed by cyberattacks on critical infrastructure requires a comprehensive and adaptive approach. This approach addresses interconnectedness, modernises outdated systems, and reduces the likelihood of human error. By implementing effective risk management strategies encompassing prevention, detection, response, resilience, and compliance, your business can safeguard critical infrastructure from the growing cyber threats of our time. At The Risk Station, we offer tailored solutions for various industries and sub-industries that contain more than 50 key risk descriptions. These solutions can help your business reduce your cybersecurity, and human error risk exposure. To learn more about our solutions, please check out our shop to embrace a proactive stance and help your organisation anticipating future risks, adapt its strategies, and remain resilient in the face of the unknown.





